Table Of Contents


Author-Maria Thompson
In this increasingly hyperconnected world, a single click can open the door to opportunity or risk. So, in this digital battlefield, every business, big or small, is a potential target. That's why Cyber Security for Businesses is no longer a technical afterthought; it’s a frontline strategy that protects your data and future.
In this blog, we'll explore what Cyber Security for Businesses truly means, the risks to watch for and the essential steps to stay protected and resilient. So read on and stay one step ahead of digital danger.
Why is Cyber Security Important for Business?
Here are the main reasons why Cyber Security for Businesses is important:

1) It protects sensitive data like customer info, financial records and trade secrets
2) It prevents costly cyberattacks that can shut down your systems or steal money
3) It builds customer trust by keeping their personal information safe
4) It keeps business running smoothly by reducing downtime and disruptions
5) It meets legal and industry rules for data protection and privacy
6) It safeguards your brand reputation from the damage of data breaches
Types of Cyber Threats
Recognising common cyber threats is crucial for Security Administrators, particularly when strengthening protection for small and medium-sized businesses. Below are some of the most frequent threats organisations encounter:
1) Phishing Attacks
Phishing involves fraudulent attempts to obtain sensitive details such as usernames, passwords or financial information by pretending to be a trusted source. These attacks are commonly delivered through spoofed emails, text messages (Smishing) or fake websites that closely resemble legitimate platforms, tricking users into revealing confidential data.
2) Ransomware
Ransomware is a kind of malicious software that encrypts files or locks systems, demanding payment in exchange for restored access. It often spreads through phishing emails or compromised websites and can severely disrupt operations, particularly if secure backups are unavailable.
3) Malware
Malware (malicious software) is a broad term covering threats such as viruses, worms, and Trojan horses. It may steal, alter or delete data, disrupt system operations, or secretly monitor user activity without consent.
4) SQL Injection
SQL Injection targets database-driven applications by inserting harmful SQL code into input fields. This can allow attackers to access, manipulate or extract sensitive business data, including customer records and confidential company information.
5) Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks
DoS and DDoS attacks aim to overwhelm a system, server or network with excessive traffic, rendering it unavailable to legitimate users. DDoS attacks involve multiple compromised systems working together to intensify the disruption.
6) Man-in-the-Middle (MitM) Attacks
MitM attacks occur when a cybercriminal secretly intercepts communication between two parties. By inserting themselves into the exchange, attackers can monitor, alter, or steal data. These attacks often occur on unsecured public Wi-Fi networks.
Become the pillar of digital trust, security and expertise for your organisation. Sign up for our Certified Data Protection Officer (CDPO) Training now!
Companies Affected by Cyber-attacks and Data Breaches
Many well-known companies have faced serious problems due to cyberattacks and data breaches. Here are two major examples that show why Cyber Security is so important:
1) British Airways
In 2018, British Airways suffered a data breach that affected around 500,000 customers. Hackers stole names, credit card details, and other personal data. The company was later fined £20 million by regulators, and the incident significantly impacted customer trust.
Key Takeaways:
a) Over 500,000 customer records stolen
b) Huge financial penalty from regulators
c) Damaged brand reputation
2) TalkTalk
TalkTalk, a UK telecom provider, was hit by a cyber-attack in 2015. Hackers accessed the personal data of over 157,000 customers. The company lost customers and paid a substantial financial penalty due to inadequate security measures.
Key Takeaways:
a) 15,000 customer records breached
b) Company fined £400,000
c) Customers lost confidence in the brand
Benefits of Effective Cyber Security for Business
Implementing strong Cyber Security measures delivers several key benefits for organisations:
1) Business Protection: Cyber Security solutions safeguard systems, networks and data from threats such as adware and ransomware. This reduces the risk of operational disruption.
2) Improved Productivity: Malware and viruses can severely slow down systems, thus affecting performance and workflow. Effective security controls help maintain system efficiency and ensure smooth day-to-day operations.
3) Better Customer Trust: Demonstrating reliable protection against cyber breaches reassures customers that their personal and financial information is handled securely. This strengthens brand credibility.
4) Customer Data Protection: Securing business systems also protects customers from indirect exposure to cyber incidents arising from compromised platforms.
5) Website and Revenue Continuity: For businesses managing their own websites, strong security prevents downtime caused by cyber attacks. This helps avoid lost transactions, reputational damage and revenue loss.
Defend digital boundaries smartly with our Certified EU General Data Protection Regulation (EU GDPR) Foundation Course – Join today!
Top 10 Cyber Security Tips for Every Business
Here are the top Cyber Security tips every business should follow to stay safe from online threats and protect their data: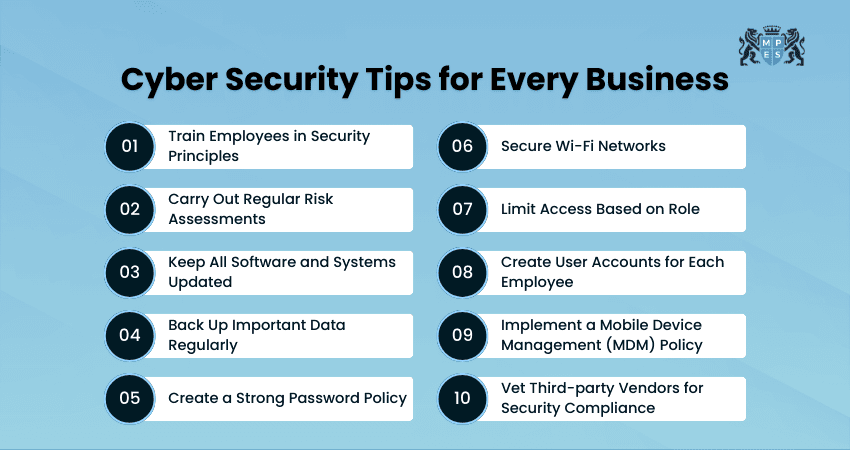
1) Train Employees in Security Principles
Employees are often the first line of defence against cyber threats. Training them in basic security practices can prevent common attacks like phishing. Make sure they know how to handle emails, links, and data securely. Ongoing training keeps them alert and updated on new risks. Try these:
a) Run regular cyber awareness sessions
b) Use quizzes and simulations for training
c) Share real-world examples of threats
2) Carry Out Regular Risk Assessments
Knowing your risks is the first step to preventing them. Regular risk assessments help you identify weak points in your systems. This lets you fix problems before they blow up into big issues. Review your risk strategy at least once a year. Take these steps:
a) Identify high-risk systems and data
b) Test for software vulnerabilities
c) Document and update findings regularly
3) Keep All Software and Systems Updated
Outdated software is a major security risk. Cyber attackers target old versions with known weaknesses. Always install updates and patches as soon as they are released. This applies to apps, systems, and devices. Take these steps:
a) Enable auto-updates where possible
b) Assign someone to manage updates
c) Track update schedules for all devices
4) Back Up Important Data Regularly
Data backups can save your business if files are lost or stolen. Set up regular automatic backups for critical data. Store backups in different locations for safety. Test your backups to make sure they work. Consider these steps:
a) Use Cloud and physical backup methods
b) Back up files daily or weekly to support Business Process Management
c) Check backup logs regularly
5) Create a Strong Password Policy
Weak passwords are easy to crack. Set rules for using long, complex passwords with letters, numbers, and symbols. Change passwords regularly and never reuse them. A clear policy makes it easier to follow safe practices. Take these steps:
a) Require minimum password length and strength
b) Enforce password changes every 90 days
c) Ban common or reused passwords
6) Secure Wi-Fi Networks
Wi-Fi networks can be entry points for Hackers if not protected. Use strong passwords and encryption for your network. Hide the network name and limit who can join. Secure Wi-Fi keeps your internal systems safe.
a) Change default router passwords
b) Use WPA3 encryption where available
c) Disable guest networks if unused
7) Limit Access Based on Role
Not everyone needs access to all systems. Give employees access only to the data they need. This limits the damage if an account is hacked. Use role-based access to stay organised and secure.
a) Set permissions by department
b) Review access levels regularly
c) Remove access for ex-employees
Simplify compliance challenges with ease in our Personal Data Protection Bill Training – Join today!
8) Create User Accounts for Each Employee
Shared accounts are a major security risk. Give every employee their own account with unique credentials. This makes it easier to track activity and manage access. Disable accounts quickly when someone leaves the company.
a) No shared logins for any system
b) Use access logs for monitoring
c) Deactivate inactive accounts promptly
9) Implement a Mobile Device Management (MDM) Policy
Mobile devices can be a weak link if not managed well. An MDM policy helps control apps, settings, and data on company phones. It also allows remote wiping of data if a device is lost. This keeps your business information safe on the go.
a) Set security settings for all devices
b) Block unauthorised apps and downloads
c) Enable remote lock and wipe features
10) Vet Third-party Vendors for Security Compliance
Vendors with access to your systems can pose risks. Check their security policies before working with them. Make sure they meet your standards for data protection. Ongoing monitoring is also important.
a) Ask for their security certifications
b) Include security terms in contracts
c) Audit vendor practices regularly
Real World Examples of Cyber Security Breaches in Small Businesses
In recent years, the growing sophistication of cyber threats has led to several high-profile breaches affecting small businesses. This underscores the need for strong security measures. Consider these examples:
1) Retail Business Example
A small boutique retailer experienced a major data breach after cybercriminals exploited weaknesses in an outdated point-of-sale system. Thousands of customer credit card details were compromised, leading to financial penalties, reputational damage, and a significant loss of customer confidence.
2) Law Firm Example
A local law firm fell victim to a phishing attack that targeted its employees. The breach exposed confidential client information, triggering legal complications and undermining trust. These examples highlight how vulnerable small businesses can be to cyber risks and spotlight the importance of updated security controls and employee awareness training.
Conclusion
More than a technical shield, Cyber security is a strategic investment in your business’s longevity. By strengthening defences and nurturing a security‑first culture, you can keep threats at bay and your customer's and employee's trust intact. In a world where digital risks evolve daily, your commitment to Cyber Security for Businesses becomes the true competitive advantage.
Turn data protection into your biggest skill with our GDPR Training – Join today and protect sensitive data effortlessly!
Frequently Asked Questions
Q. How is Cyber Security Used in Business?
Cyber Security is used in business to protect systems, networks, devices and sensitive data from unauthorised access and cyber attacks. It helps organisations secure customer information, financial records and intellectual property. This is done via firewalls, encryption, access controls, monitoring tools and employee awareness training.
Q. What are the Four Pillars of Cyber Security?
The four core pillars are:
a) Confidentiality: Making sure sensitive information is accessible only to authorised individuals.
b) Integrity: Protecting data from unauthorised alteration.
c) Availability: Ensuring systems and data remain accessible when needed.
d) Accountability: Tracking user actions to maintain transparency.
Q. What is the Golden Rule of Cyber Security?
The golden rule of Cyber Security is: Never trust, always verify. This principle means that no user, device or system should be automatically trusted. Every access request must be authenticated before being granted.
 Have Any Question?
Have Any Question?
 +44 7452 122728
+44 7452 122728





 Back
Back








 44 7452 122728
44 7452 122728